Author Archives: DHX Software

Understanding the Core Learning Management System Functions
Companies looking to establish a robust employee training system may be looking into several options, including a learning management system (LMS).
LEARN MORE
The Benefits Of A “Full-Service” LMS Partner
A full-service LMS partner can help you launch or improve your eLearning system by creating, maintaining, and hosting a learning management system (LMS).
LEARN MORE
Custom Field Service Management Software to Grow Profits & Efficiency
High-caliber scheduling and field management software will improve your company’s overall efficiency and increase your profits.
LEARN MORE
Training Content Development Guide for Effective Programs
If your employees complain about boring training programs that don’t engage them, you might need to beef up your training content. Strong content development
LEARN MORE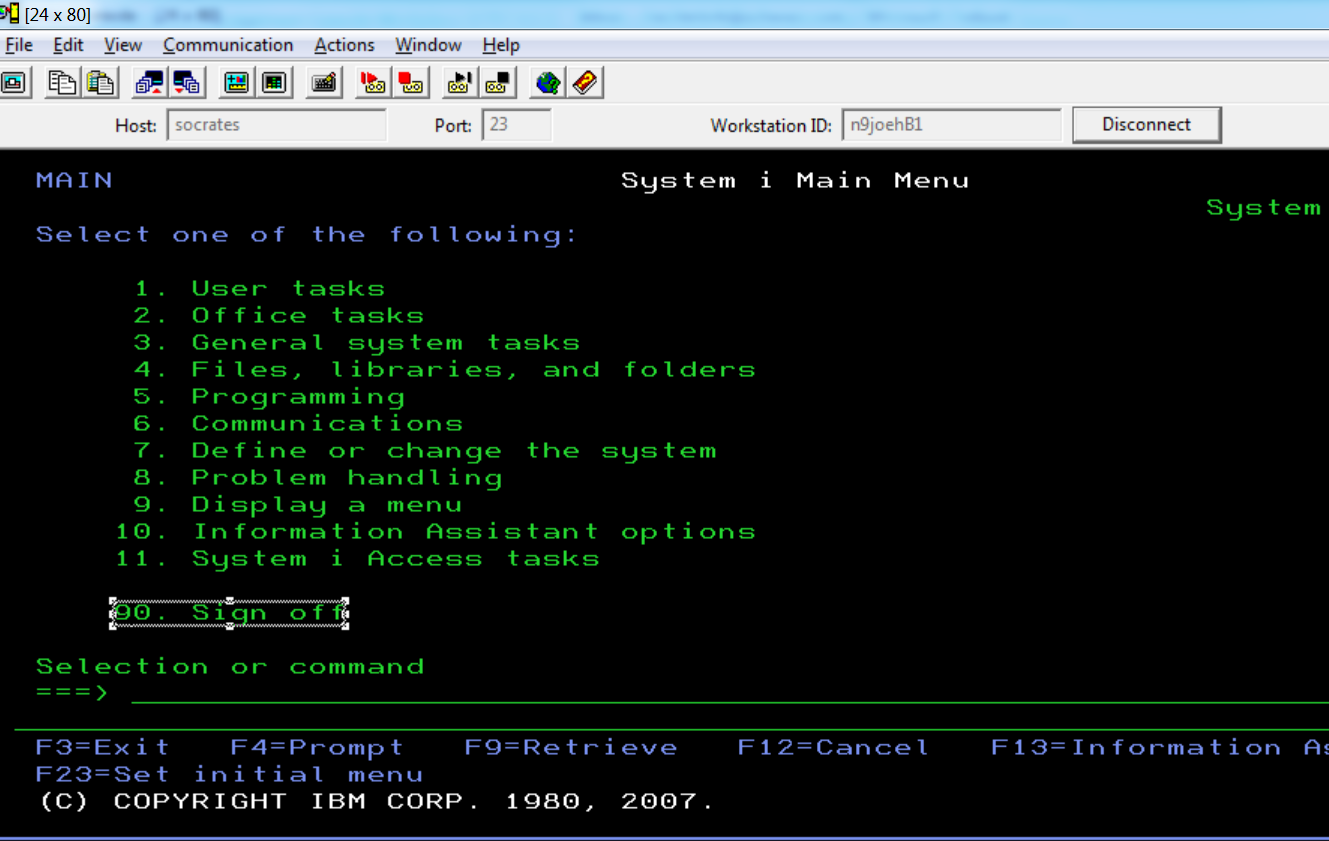
Contemporize Legacy Apps with Application Modernization
As we network around Phoenix, we run into lots of very successful companies in a range of industries, including retail, distribution, manufacturing
LEARN MORE
Compliance Training With Efrontpro Technology For Financial Services
Exchange Analytics, Inc. is a leading supplier of interactive online compliance training courses to the securities and derivatives industries.
LEARN MORE
Are you Tracking Leads and Opportunities in a Spreadsheet?
We talk a lot about how many of our customers run their business on old systems that don't necessarily talk to each other.
LEARN MORE
Custom Software Solutions Built for Business Owners
We’re guessing you will be relieved to have your business software developed by people who understand business, by people who speak your language
LEARN MORE
In-House Versus Outsourced Software Development
"There's an app for that." The claim that a software application can do almost anything is true. Today apps are used in almost every aspect of business from marketing
LEARN MORE
Protecting Legacy Systems from Cybersecurity Threats
When small business owners think about protecting legacy systems from cybersecurity threats, they most often think of hardware like routers, switches, networks
LEARN MORE